State of C 2026
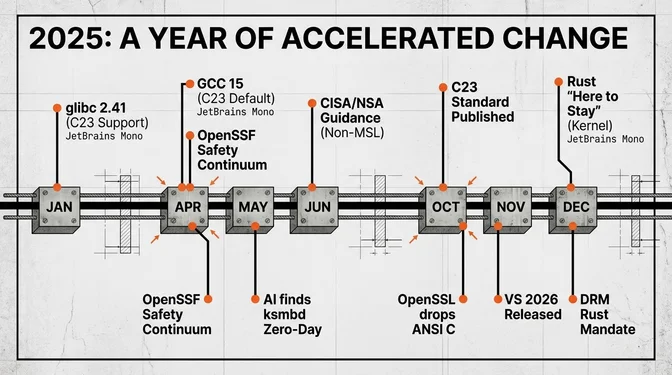
The year 2025 stands as a definitive inflection point in the half-century trajectory of C. Following the formal publication of the C23 standard (ISO/IEC 9899:2024) on October 31, 2024, the ecosystem found itself navigating a complex trilemma: maintaining the unparalleled stability required by legacy infrastructure, integrating aggressive performance demands of modern silicon through new compiler vectorization capabilities, and confronting the existential threat posed by industry-wide memory safety mandates. GCC 15's April release made C23 the default dialect (and added #embed support), accelerating C23 adoption in production toolchains. Meanwhile, the Linux Kernel Maintainers Summit declared Rust "no longer experimental," calling it "here to stay" alongside C's ~34 million lines of kernel code.
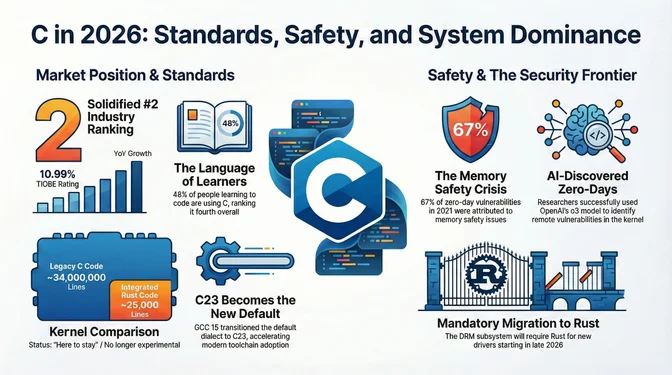
The TIOBE Index shows C at #2 with a 10.99% rating and +2.13% year-over-year change (Jan 2026 table), one of the biggest jumps among top languages. Stack Overflow's 2025 survey shows 19.1% of professional developers using C, 22% of all respondents, and 48% of learners, ranking it fourth among those learning to code. The embedded systems market remains C's stronghold, with industry surveys often citing a majority share for C in embedded projects. Yet CISA and NSA joint guidance urged prioritizing memory-safe languages for new development and treated C/C++ as typical non-MSLs, citing that 67% of zero-day vulnerabilities in 2021 were memory safety issues.
Actions for 2026: Install your distro's patched glibc for CVE-2025-4802 (upstream fixed after 2.38; most distros backport); Enable C23 mode (-std=c23) in your build systems; Integrate AddressSanitizer and OSS-Fuzz into CI pipelines; Review MISRA C:2025 guidelines for safety-critical projects; Track the C2Y standard work for defer keyword developments.
January 2025
ALGOL 68 GCC Front-End
TIOBE Index #4
ISO WG14 C2y Work Begins
CVE-2025-0395
assert() function (CVSS 7.5 via NVD / CISA-ADP, availability impact), affecting versions 2.13 through 2.40. The bug dates to 2011; Qualys discovered it and characterized it as relatively minor. GNU C Library 2.41
acospi, sinpi), a _ISOC2Y_SOURCE test macro for draft C2Y features, and AArch64 Guarded Control Stack support for enhanced security.February 2025
GNU Binutils 2.44
glibc 2.41 Compatibility Issues
curl 8.12.0
.netrc passwords to the wrong host during HTTP redirects.Rust-in-Linux Friction
CVE-2025-26519
ISO WG14 Meeting in Graz
union removal.March 2025
TIOBE Index #4
LLVM 20.1.0
MISRA C:2025
VS Code C/C++ Performance
April 2025
GCC 15 in Fedora 42
GCC 15.1
gnu17 to gnu23, the first default change in years. The release included experimental C2y feature support (generic selection expressions N3260, named loops N3355), significant OpenMP improvements for GPU offloading, a new COBOL front-end, and improved experimental Rust front-end (gccrs). Red Hat documented the #embed directive implementation.Memory Safety Continuum
May 2025
CVE-2025-4802
LD_LIBRARY_PATH in setuid binaries. Affecting versions 2.27-2.38, it allowed loading malicious libraries in statically compiled setuid programs.GitHub Copilot Coding Agent
CVE-2025-37899 (AI-Discovered)
June 2025
RedMonk Rankings
CISA/NSA Memory Safety Guidance
July 2025
CVE-2025-8058
regcomp function (CVSS 5.9 v4, CNA score; Gentoo rated High), affecting versions 2.4-2.41.GNU C Library 2.42
Stack Overflow 2025 Survey
August 2025
GCC 15.2
CVE-2025-8941
LLVM 21.1
September 2025
CppCon 2025
Gentoo Security Advisory
CVE-2025-39869
sizeof(s8) and pointer mismatch causing memory corruption on ARM platforms.Safe C++ Abandoned
OpenSSL Vulnerabilities
October 2025
TIOBE Index #2
VS Code C23 IntelliSense Support
bool type and the true/false keywords (N2935).vcpkg Growth
WG14 C2y Submissions
GitHub Octoverse
November 2025
SQLite 3.51.0
Visual Studio 2026
Zephyr RTOS 4.3.0
December 2025
CLion 2025.3
Rust "Here to Stay" in Linux
CVE-2025-13912
__builtin_ct_select intrinsics, targeting an upcoming release.gccrs Linux Kernel Goal
DRM Rust Mandate
Conan 2.24.0
First Rust Kernel CVE
rust_binder). For perspective, NVD assigned 159 CVEs to C code the same day.GitHub Copilot C++ Tools
GDB 17.1
curl's Best Year
Security, Vulnerabilities, and Mitigations
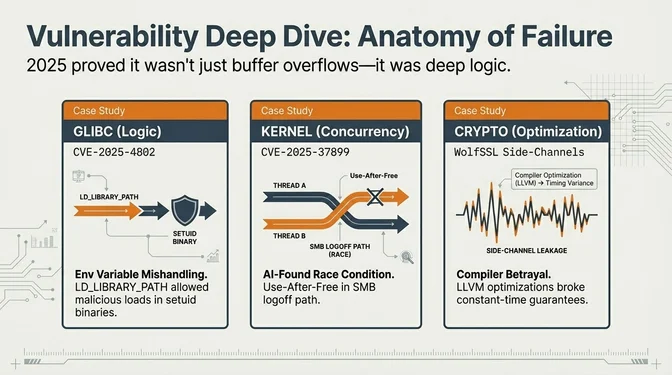
2025's most consequential incidents were deep-logic flaws rather than trivial overflows. The standout example was CVE-2025-37899 in Linux ksmbd, found with OpenAI's o3 by Sean Heelan (Heelan frames it as remote; NVD currently scores AV:L/PR:L). Core infrastructure saw high-impact bugs too: glibc (CVE-2025-4802, CVE-2025-0395, CVE-2025-8058), OpenSSL (CVE-2025-9230, CVE-2025-9231, CVE-2025-9232), and system plumbing like musl (CVE-2025-26519), curl (CVE-2025-0167), and linux-pam (CVE-2025-8941). Kernel and compiler edge cases added more uncertainty: CVE-2025-39869 (CVSS pending), CVE-2025-13912 (wolfSSL compiled with LLVM), and the first Rust kernel CVE (CVE-2025-68260).
Mitigations pushed both runtime hardening and safer coding paths. The kernel continued ARM MTE and heap quarantine work, while library ecosystems kept patching actively; for example, libpng 1.6.51 fixed security issues including CVE-2025-65018 (libpng 2025 news). Toolchain support also advanced: Trail of Bits proposed constant-time support for LLVM with __builtin_ct_select, and a 2025 Checked C experience paper on EDK II reported progress on spatial memory safety.
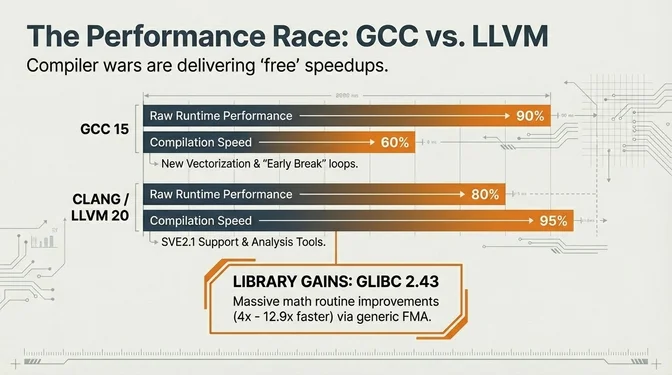
Performance and the Compiler Race
The GCC vs. Clang rivalry delivered tangible speedups. Phoronix benchmarks showed GCC 15 with a small edge in raw runtime performance and Clang 20 with faster compiles, while GCC's new "early break" loop vectorization unlocked SIMD gains in text-heavy workloads. On ARM, LLVM 20 added SVE2.1 support for scalable vectorization across server chips.
Library and runtime performance kept improving: glibc 2.42 shipped math and malloc tuning, and Phoronix reported upcoming glibc 2.43 work with 4× and 12.9× math gains tied to a new generic FMA implementation. The Language Benchmarks Game continued to show C trading the speed crown with C++ and Rust.
Ecosystem Signals and Release Cadence
Adoption signals stayed strong even amid volatility: the TIOBE index had C at #2 (10.99%, +2.13 YoY), and the Stack Overflow 2025 survey showed 19.1% of professional developers and 48% of learners using C. Embedded remains the stronghold; the FOSDEM 2025 embedded track emphasized the economic cost of migrating certified C codebases in automotive and aerospace.
Major releases reinforced the ecosystem's breadth: SQLite 3.50.0/3.51.0, curl shipping eight releases, OpenSSL 3.5 LTS and 3.6, RTOS updates like FreeRTOS and Zephyr, and toolchain drops from GCC, LLVM, CMake, and Meson. MISRA also advanced with MISRA C:2025, adding 225 guidelines and clarifying AI-generated code treatment.
Tooling Momentum and Standards Politics
AI-enhanced tooling became normal: Visual Studio 2026 shipped deep Copilot integration, the VS Code C/C++ extension added Copilot Hover, and CLion 2025.3 moved to its Nova engine. Build and package tools kept pace via CMake 4.0, Meson 1.10.0, Conan 2.24.0, and vcpkg, while debugging stacks improved with GDB 17.1 and Valgrind 3.25.0.
Standards and governance stayed contentious. WG14's C2y work focused on correctness and cleanup via papers like "Slay Some Earthly Demons", with future meetings scheduled on the WG14 calendar and ongoing draft tracking in the C2Y projects list. At the same time, TrapC (N3423) triggered backlash (see Slashdot and Reddit), the Safe C++ proposal collapsed, and Rust-in-Linux friction (including Linus Torvalds' response) underscored the governance strain.
C 2026 Watchlist
1. DRM Subsystem Rust Mandate
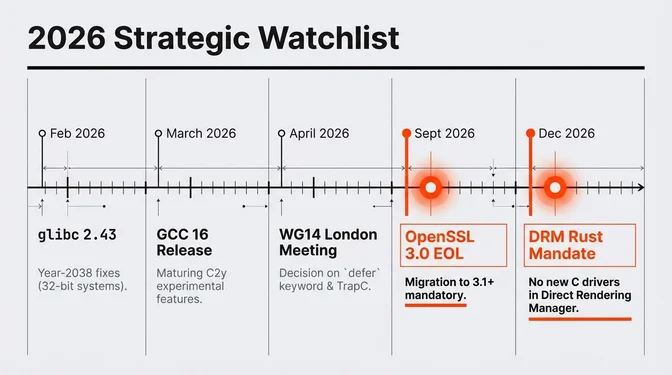
When: Approximately December 2026
Context: Dave Airlie, the DRM subsystem maintainer, announced plans to require Rust and disallow C for new DRM drivers within one year. This would mark the first major kernel subsystem to mandate a language other than C for new contributions. The kernel currently contains approximately 34 million lines of C vs. 25,000 lines of Rust.
Action: Track LKML discussions on DRM/Rust requirements. Review your organization's kernel driver development strategy. If contributing to DRM subsystem, begin Rust training.
2. GCC 16 Release
When: March-April 2026
Context: Expected to switch C++ default to C++20, mature the "experimental" C2y features introduced in GCC 15, and potentially include the ALGOL 68 front-end. The gccrs developers aim to compile the Linux kernel in Rust with GCC. If production-ready, C and Rust could mix seamlessly in the same toolchain.
Action: Test C2y features (defer, generic selection expressions, named loops) in development builds. Plan for gccrs maturity enabling mixed C/Rust projects without LLVM dependency.
3. OpenSSL 3.0 End-of-Life
When: September 2026
Context: OpenSSL 3.0 goes EOL, and OpenSSL 4.0 targets April 2026. Projects must migrate to OpenSSL 3.5 LTS or later, as intermediate 3.x releases (3.1–3.3) will already be end-of-life by the time 3.0 expires. OpenSSL 3.6.0 now requires C99 compilers; ANSI C is no longer enough.
Action: Audit all deployments using OpenSSL 3.0.x. Schedule migration to OpenSSL 3.5 LTS or later. Verify your build toolchain supports C99 or later.
4. ISO WG14 London Meeting
When: April 2026
Context: The London meeting will likely be a full committee meeting where proposals for C2y are officially adopted or rejected. WG14 will likely reject TrapC or move it to Technical Specification track. The defer keyword has GCC patches already; WG14 will likely vote on it here.
Action: Track WG14 document log for adopted proposals. If maintaining C libraries, assess impact of potential defer keyword, bounds-checked pointer proposals, or K&R function definition deprecation.
5. TIOBE Ranking Volatility
When: Throughout 2026
Context: With the gap between C (#2, 10.99%) and Java (#3) narrowing, and C#'s rapid ascent, 2026 might see C drop out of top 2 for the first time in decades. The March 2025 dip to #4 showed this volatility is possible.
Action: Use rankings for stakeholder communication, not technical decisions. C's embedded dominance (60%+ market share) and kernel criticality remain unchanged regardless of survey fluctuations.
6. glibc 2.43
When: February 2026
Context: Roadmap includes overhaul of time locale API (year-2038 issues on 32-bit systems) and possibly enabling C2y features under _ISOC2Y_SOURCE as the draft firms up.
Action: Test 32-bit systems against time-related functionality. Prepare for potential API changes affecting embedded or legacy deployments.
7. MSVC C23 Support Status
When: Throughout 2026
Context: Despite Visual Studio 2026, Microsoft has published no official C23 roadmap. Key features like _BitInt, nullptr, and #embed remain unavailable. Only partial support exists through /std:clatest. Many note MSVC still doesn't fully support C99.
Action: For cross-platform C projects, maintain GCC/Clang as primary compilers. Use MSVC conditional compilation for Windows-specific paths. Track /std:clatest improvements.
8. Embedded World 2026 & CppCon 2026
When: March (Embedded World), September (CppCon)
Context: Embedded World will showcase ongoing C vs. Rust narrative in embedded. Expect more vendors with Rust offerings but also new MISRA C:2025 guideline tooling. CppCon often covers cross-cutting topics affecting C including safety profiles that could model C's future.
Action: Watch for MISRA C:2025-compliant static analysis tool announcements. Track safety profile discussions that may influence C2y direction.
9. AI-Discovered Vulnerabilities Escalation
When: Throughout 2026
Context: CVE-2025-37899's discovery using OpenAI o3 showed AI-assisted analysis can find complex concurrency bugs in kernel C code. The DARPA "Hardening Legacy C Systems" program will release results in 2026, potentially including tools to retrofit memory safety on C binaries.
Action: Integrate AI-assisted fuzzing (AuditAI, enhanced OSS-Fuzz) into CI pipelines. Track DARPA results for practical LLVM passes or binary rewriters adding bounds checks to existing C apps.
10. musl libc 2.0
When: 2026
Context: musl 2.0 will incorporate all C23 library additions, which is important for containerized environments using lightweight libc (Alpine Linux base images).
Action: Test C23 feature usage against musl 2.0 pre-releases. Verify container-based CI/CD pipelines remain compatible.