State of Go 2026
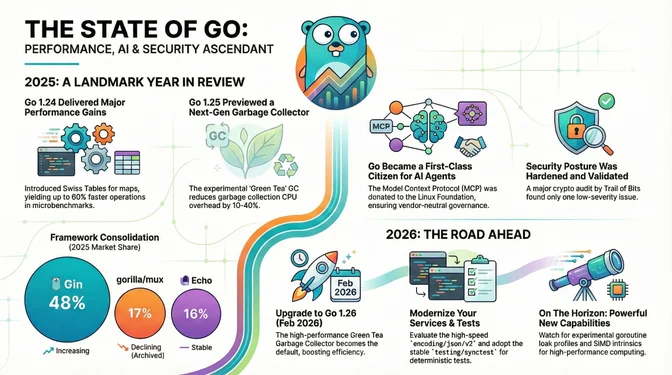
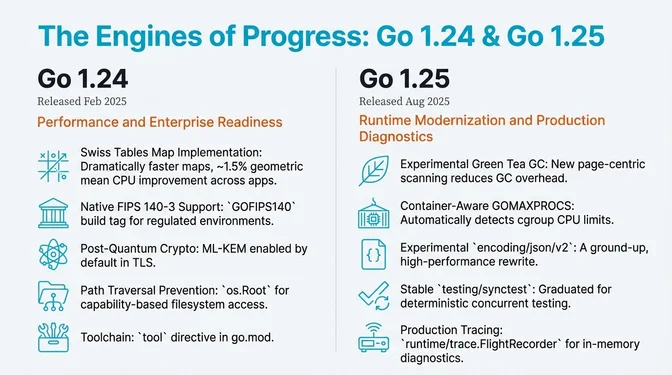
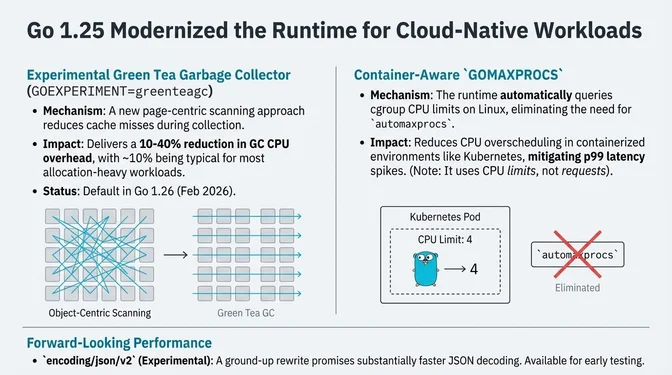
Two major releases defined Go in 2025: Go 1.24 delivered a 2–3% average runtime CPU overhead reduction, including Swiss Tables maps with up to 60% faster operations than Go 1.23 in microbenchmarks, plus native FIPS 140-3 module support, while Go 1.25 introduced the experimental Green Tea garbage collector delivering 10-40% GC overhead reduction and container-aware GOMAXPROCS that reduces overscheduling under CPU limits. Go reached #7 in the TIOBE Index (its all-time high, November 2024), and the language positioned itself as infrastructure for the AI agent era with the official Go MCP SDK, which gained industry-wide backing when Anthropic donated MCP to the Linux Foundation in December.
The year also marked Go's first under new technical leadership: Austin Clements took over as Tech Lead in September 2024 after Russ Cox stepped down from 12 years in the role, explicitly rejecting the "BDFL" model. Cherry Mui now leads Go core (compiler/runtime/releases).
The year tested the ecosystem's security posture: Go shipped frequent security point releases, including 10 fixes in a single October release, the largest security update of the year. The Trail of Bits audit found only one low-severity issue. Framework consolidation continued: Gin holds 48% while gorilla/mux declined to 17% post-archival. 70% of Go developers now use AI assistants regularly.
Actions for 2026: Test Go 1.26 RC for Green Tea GC (default in February), migrate from ingress-nginx before March 2026 retirement (Kubernetes users), review encoding/json/v2 for performance-critical JSON workloads.
Go 2025 Timeline
January 2025
Go 1.23.5
go telemetry on (local-only by default). Covers go, gopls, govulncheck. Data at telemetry.go.dev.February 2025
Go 1.23.6
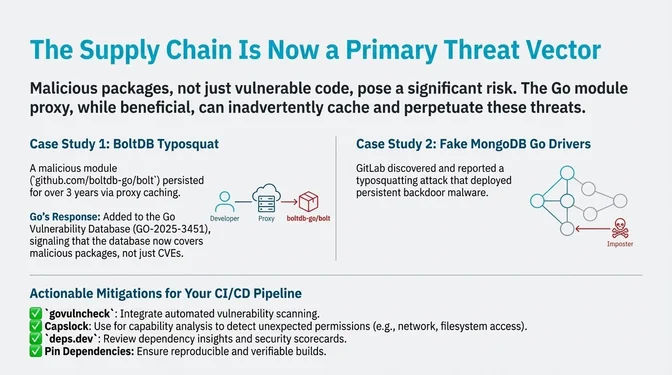
BoltDB Typosquat Disclosed
github.com/boltdb-go/bolt): a malicious module that had persisted for 3+ years via Go module proxy caching. Added to Go Vulnerability Database as GO-2025-3451. Google removed it from the proxy and recommended Capslock capability analysis for supply chain defense. Go 1.24.0
GOFIPS140 environment variable and GODEBUG=fips140=on (set before program start; v1.0.0 is In-Process/Review Pending; no completed CMVP validations yet) - Generic type aliases: Full support for parameterized type aliases - Tool dependencies in go.mod: New tool directive with go get -tool - os.Root: Directory-scoped filesystem operations preventing path traversal attacks - testing.B.Loop: Cleaner benchmark iteration syntax - runtime.AddCleanup: Modern finalization replacing SetFinalizer - testing/synctest (experimental): Deterministic concurrent code testing - Weak pointers: New weak.Pointer type for cache implementations - New crypto packages: crypto/mlkem (post-quantum), crypto/hkdf, crypto/pbkdf2, crypto/sha3gopls v0.18.0
modernize, unusedfunc, hostport, gofix. Added "Go to Implementations" support for generics.March 2025
Go 1.23.7 and Go 1.24.1
Delve v1.24.1
Uber PGO Case Study
April 2025
Go 1.23.8 and Go 1.24.2
May 2025
GopherCon Latam 2025
Go 1.23.9 and Go 1.24.3
Trail of Bits Crypto Audit
GopherCon Israel 2025
June 2025
Error Handling Syntax Efforts Halted
if err != nil remains.Go 1.23.10 and Go 1.24.4
gopls v0.19.0
GopherCon Europe 2025
Azure SDK for Go
July 2025
Go 1.23.11 and Go 1.24.5
Microsoft Go Telemetry
MS_GOTOOLCHAIN_TELEMETRY_ENABLED=0. Relevant for orgs using Microsoft's Go build for FIPS compliance/system-crypto requirements.August 2025
Go 1.23.12 and Go 1.24.6
Go 1.25.0
GOEXPERIMENT=greenteagc): 10-40% GC overhead reduction through page-centric scanning - Container-aware GOMAXPROCS: Runtime automatically queries cgroup CPU limits on Linux (note: uses limits, not requests) - encoding/json/v2 (experimental): Ground-up rewrite with substantially faster decoding - testing/synctest graduated to stable: Deterministic concurrent testing (old experiment API removed in Go 1.26) - Core types removed: Language spec simplification - runtime/trace.FlightRecorder: Rolling in-memory trace buffer for production diagnostics - sync.WaitGroup.Go: Convenient goroutine creation with automatic Add/Done - DWARF version 5: Smaller binaries and faster linking - net/http CrossOriginProtection: Built-in CSRF defense - Platform updates: Requires macOS 12+; 32-bit windows/arm marked for removalMicrosoft Go 1.25
systemcrypto backend. Complements upstream FIPS module with a different approach to regulated crypto requirements.GopherCon UK
GopherCon US 2025
September 2025
Go 1.24.7 and Go 1.25.1
GopherCon India 2025
October 2025
GoLab 2025
Go 1.24.8 and Go 1.25.2
| CVE | Package | Issue | |
|---|---|---|---|
| CVE-2025-47912 | net/url | Insufficient validation of bracketed IPv6 hostnames | |
| CVE-2025-58183 | archive/tar | Unbounded allocation parsing GNU sparse maps | |
| CVE-2025-58185 | encoding/asn1 | Memory exhaustion from malformed DER | |
| CVE-2025-58186 | net/http | Unlimited cookie parsing causing large allocations | |
| CVE-2025-58187 | crypto/x509 | Non-linear name constraint checking | |
| CVE-2025-58188 | crypto/x509 | Panic validating DSA public keys | |
| CVE-2025-58189 | crypto/tls | Error containing unescaped attacker data | |
| CVE-2025-61723 | encoding/pem | Non-linear parsing time | |
| CVE-2025-61724 | net/textproto | Excessive CPU in ReadResponse | |
| CVE-2025-61725 | net/mail | Excessive CPU parsing domain-literals |
GoWest 2025
GopherCon Africa 2025
November 2025
Go 1.24.10 and Go 1.25.4
Go 16th Anniversary
golang.org/x/crypto/ssh CVEs
govulncheck Update
Go 1.26 Development Freeze
December 2025
Go 1.24.11 and Go 1.25.5
MCP Donated to Linux Foundation
Delve v1.26.0
savestate command, and follow-exec mode.Rob Pike AI Email Response
Performance Improvements Summary
Go 1.24: Swiss Tables and Baseline Gains
| Optimization | Improvement | Source |
|---|---|---|
| Map operations (microbenchmarks) | Up to 60% faster than Go 1.23 | Go Blog |
| Full-app CPU (geometric mean) | ~1.5% improvement | Go Blog |
| sync.Map | Reduced contention (concurrent hash-trie) | Go 1.24 Notes |
| AES-CTR (amd64/arm64) | Several times faster | [Go 1.24 Notes](https://go.dev/doc/go1.24) |
|---|---|---|
| crypto/rand (Linux 6.11+) | Several times faster (vDSO) | Go 1.24 Notes |
Production validation: Datadog reported hundreds of gigabytes of memory savings from Swiss Tables in high-traffic services after the Go team resolved the initial RSS regression.
Go 1.25: Green Tea GC and Runtime
| RSA on WebAssembly | Up to 2x faster | [Go 1.24 Notes](https://go.dev/doc/go1.24) |
|---|---|---|
| Optimization | Improvement | Source |
| GC overhead (experimental) | 10-40% reduction (~10% typical) | Go Blog |
| encoding/json/v2 decoding | Substantially faster | [Go 1.25 Notes](https://go.dev/doc/go1.25) |
|---|---|---|
| FIPS 140-3 module | Avoids cgo/FFI overhead, cross-compiles cleanly | Go Blog |
Ecosystem Metrics (2025)
Adoption Statistics
| Metric | Value | Source |
|---|---|---|
| Developer satisfaction | 93% | Go Developer Survey |
| AI assistant usage | 70% of developers | Go Developer Survey |
| TIOBE Index ranking | #7 (all-time high, Nov 2024) | InfoWorld |
Framework Market Share
| Framework | Share | Trend |
|---|---|---|
| Gin | 48% | Up from 41% (2020) |
| net/http (stdlib) | - | Growing with 1.22 routing |
| gorilla/mux | 17% | Down from 36% (archived 2023) |
| Echo | 16% | Stable |
| chi | ~12% | Rising |
| Fiber | 11% | Stable (fasthttp-based) |
Source: JetBrains
Security Overview (2025)
CVE Summary
Go shipped frequent security point releases in 2025, including a 10-fix release on October 7, the largest single security update of the year. More fixes addressed vulnerabilities in golang.org/x/crypto and x/net.
Supply Chain Attacks
2025 exposed Go module ecosystem vulnerabilities beyond CVEs:
- BoltDB typosquat (
github.com/boltdb-go/bolt): Malicious module persisted 3+ years via proxy caching. Added to Go Vulnerability Database (GO-2025-3451), a policy signal that the vuln DB covers malicious packages, not just CVEs. - Fake MongoDB Go drivers: GitLab caught typosquatting attack deploying persistent backdoor malware.
Mitigations: Capslock capability analysis, deps.dev dependency insights, govulncheck in CI, SLSA/OpenSSF attestations.
Notable Security Achievements
- Trail of Bits audit: Only one low-severity issue in Go cryptography
- FIPS 140-3 module support: Native implementation with
GOFIPS140andGODEBUG=fips140=on(v1.0.0 In-Process/Review Pending; check status) - CSRF protection: Built-in net/http CrossOriginProtection
- Post-quantum cryptography: X25519MLKEM768 enabled by default when
tls.Config.CurvePreferencesis nil (disable withGODEBUG=tlsmlkem=0) - Path traversal prevention: os.Root capability-based filesystem API
AI and MCP Ecosystem
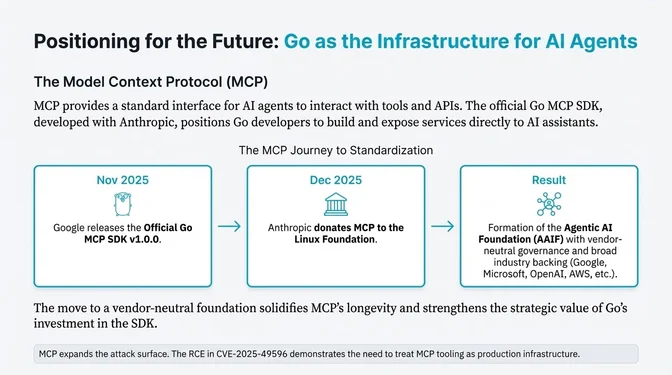
The Model Context Protocol (MCP) enables AI agents to interact with tools, APIs, and codebases through a standardized interface. Go's official SDK and experimental gopls integration position Go developers to build and expose services to AI assistants.
In December 2025, Anthropic donated MCP to the Linux Foundation, establishing the Agentic AI Foundation (AAIF) with vendor-neutral governance. Co-founded by Anthropic, Block, and OpenAI; platinum members include AWS, Bloomberg, Cloudflare, Google, and Microsoft. Adoption spans ChatGPT, Cursor, Gemini, Copilot, and VS Code, with 10k+ published MCP servers. This strengthens the long-term viability of Go's MCP investment.
| Development | Description | Source |
|---|---|---|
| Go MCP SDK v1.0.0 | Official SDK with Anthropic collaboration | Go Blog |
| gopls MCP integration | Experimental MCP server in gopls | Go Blog |
| MCP → Linux Foundation | Vendor-neutral governance via AAIF | Anthropic |
| Ollama | ~160k stars (as of Jan 2026), leading local LLM project | GitHub |
Security note: MCP tooling expands attack surface. CVE-2025-49596 (MCP Inspector < 0.14.1) showed RCE risk from missing auth between inspector and proxy. Treat MCP tooling like production infrastructure: pin versions, patch quickly, sandbox, apply least privilege.
Go 2026 Watchlist
1. Go 1.26 Release
When: February 2026. RC1 released December 16, 2025.
Context: Go 1.26 (from draft release notes; subject to change) brings Green Tea GC as default, ~30% faster baseline cgo calls, new(expression) syntax, experimental SIMD intrinsics, crypto/hpke, revamped go fix command, and experimental goroutine leak profiles. Last release supporting macOS 12 Monterey; Windows 32-bit ARM removed.
Action: Test RC now. Benchmark GC-heavy workloads for Green Tea improvements. Audit cgo-heavy code for performance gains.
2. Green Tea GC Migration
When: February 2026 (default in Go 1.26). Already available via GOEXPERIMENT=greenteagc in Go 1.25.
Context: The Green Tea GC shifts from object-centric to page-centric scanning, reducing cache misses during collection. Benchmarks show ~10% typical / up to 40% reduction in GC CPU overhead for allocation-heavy workloads. Opt-out removal expected in Go 1.27.
Action: Enable GOEXPERIMENT=greenteagc in staging now. Track GC metrics (runtime.ReadMemStats). Report issues before default enablement.
3. encoding/json/v2 Evaluation
When: Available now via GOEXPERIMENT=jsonv2. GA expected Go 1.27 or later.
Context: encoding/json/v2 is a ground-up rewrite with substantially faster decoding, configurable marshaling, and streaming support via jsontext.
Opt-in enables legacy API to use new engine. See jsonbench for detailed benchmarks.
Action: Benchmark JSON-heavy workloads with GOEXPERIMENT=jsonv2. Test edge cases with custom marshalers. Plan migration path for performance-critical services.
4. Container-Aware GOMAXPROCS
When: Now. Stable in Go 1.25.
Context: Container-aware GOMAXPROCS automatically adjusts based on cgroup CPU limits (not requests), reducing overscheduling in Kubernetes and mitigating p99 spikes in some workloads. Caveats: does not consider CPU requests; disabled if you set GOMAXPROCS manually.
Action: Remove automaxprocs dependency if running Go 1.25+. Don't set GOMAXPROCS explicitly unless needed. Verify GOMAXPROCS reflects container limits in production.
5. testing/synctest Adoption
When: Now. Stable in Go 1.25; old experiment API removed in Go 1.26.
Context: testing/synctest virtualizes time inside "bubble" environments, making concurrent tests deterministic. time.Sleep(1 * time.Hour) advances virtual clock instantly when all goroutines block.
Action: Migrate flaky time-dependent tests to synctest before Go 1.26 removes old API. Remove arbitrary sleeps and retry loops in test suites.
6. SIMD Intrinsics (Experimental)
When: Go 1.26 (February 2026). Behind GOEXPERIMENT=simd.
Context: simd/archsimd provides architecture-specific SIMD intrinsics (128-bit to 512-bit vectors on amd64). First step toward high-level portable SIMD.
Action: Identify compute-intensive workloads (image processing, ML inference, compression). Review experimental API for performance-critical paths.
7. goroutine Leak Detection
When: Go 1.26 (experimental). Default expected Go 1.27.
Context: goroutine leak profiles detect leaked goroutines in production, a long-requested diagnostic capability.
Action: Enable leak detection in staging. Integrate with existing pprof workflows. Identify and fix leak sources before production rollout.
8. FIPS 140-3 Adoption
When: Now. Available since Go 1.24.
Context: FIPS 140-3 module support facilitates compliance for regulated industries. Build with GOFIPS140=v1.0.0 go build, enable at runtime with GODEBUG=fips140=on (or only for stricter mode). Caveats: enabling FIPS mode alone may not meet all regulatory requirements; v1.0.0 is In-Process/Review Pending with no completed CMVP validations yet.
Action: For regulated environments: test FIPS mode with GODEBUG=fips140=on. Build production binaries with GOFIPS140=v1.0.0. Consult compliance officers, as FIPS mode is necessary but may not be enough.
9. Go 1.27 Roadmap
When: August 2026.
Context: Likely based on current direction: Green Tea GC opt-out removal, goroutine leak profiles default, encoding/json/v2 toward GA, continued SIMD expansion. These are projections, not confirmed plans.
Action: Track accepted proposals. Plan for deprecated GODEBUG settings from Go 1.22/1.23 era removal.
10. Framework Migration Decisions
When: Review in 2026.
Context: net/http routing enhancements in Go 1.22 reduced third-party router necessity. Gin at 48%, gorilla/mux declining post-archival. chi gaining share as stdlib-compatible option.
Action: Review stdlib routing for new services. Consider migration from gorilla/mux to chi or stdlib. Assess framework choice based on team familiarity and feature requirements.
11. AI/MCP Integration
When: Ongoing. Official Go MCP SDK v1.0.0 available. MCP now under Linux Foundation governance.
Context: Go MCP SDK released with Anthropic collaboration. MCP donated to Linux Foundation (AAIF) in December 2025 for vendor-neutral governance. Experimental gopls MCP server integration enables IDE-to-agent protocol. Go positioned as infrastructure for AI agent development.
Action: Review MCP SDK for exposing Go APIs to AI agents. Test gopls MCP integration in development workflows. Treat MCP tooling as production infrastructure: CVE-2025-49596 showed early security risks.
12. Security Posture
When: Ongoing. Frequent point releases in 2025.
Context: Go shipped 10 security fixes in a single October release, plus more fixes throughout the year, mostly moderate-severity DoS vulnerabilities.
Trail of Bits audit validated cryptography. Supply chain attacks (BoltDB typosquat, fake MongoDB drivers) highlighted module ecosystem risks.
Action: Maintain rapid patching cadence. Enable govulncheck in CI. Consider Capslock for capability analysis. For FIPS requirements: build with GOFIPS140=v1.0.0 and enable GODEBUG=fips140=on.
13. Toolchain Workflow Changes
When: Now through Go 1.26.
Context: Go 1.24-1.26 introduced notable workflow changes: tool directive in go.mod, GOAUTH for private modules, go.mod ignore directive, go doc -http mode, go version -m -json, and revamped go fix command.
Action: Review Go 1.24, Go 1.25, and Go 1.26 release notes for workflow changes applicable to your projects.